In today’s competitive landscape, demonstrating robust security practices is no longer a nicety; it’s a necessity. Achieving SOC 2 certification by an independent third-party auditor is a powerful way to showcase your commitment to data security and gain a strategic edge. However, navigating the complexities of the SOC 2 journey can feel daunting. Here’s where a SOC 2 compliance readiness partner steps in. A SOC 2 readiness partner acts as your trusted guide, providing the expertise and support you need to achieve compliance efficiently and effectively.
Working with a SOC 2 Compliance Readiness Partner not only provides reasonable assurance to achieve your SOC 2 compliance but also prepares your organization for a SOC 2 Audit. The SOC 2 Audit is part of a SOC 2 Examination, which results in a SOC 2 Report. While this is not technically a certification process, it is often referred to as one because of the impartiality of the SOC 2 auditor, the thoroughness of their evaluation, and the details in their SOC 2 Report. A favorable SOC 2 Report proves your compliance with AICPA‘s Trust Services Criteria and helps you unlock the doors to new business, check many of the RFP (Request For Proposal) requirements, strengthen client trust and, ultimately, accelerate your revenue growth.
Security experts at databrackets have supported various clients as their SOC 2 Compliance Readiness Partner. We have worked with SaaS Providers, MSPs, Start-ups, Healthcare Providers, Radiology Organizations, Pharmaceutical Companies, Financial Services & Accounting Firms, Law Firms, Insurance Firms, etc. Our experience across industries has been possible because of our customized approach and focus on evidence collection and documentation, which CPAs need during a SOC 2 Audit. We have worked closely with various CPA partner firms and ensure they receive documentation in a systematic manner through dbACE, our GRC Platform. Additionally, clients have the option to engage their own CPA firm for their SOC 2 Examination, with databrackets serving as their readiness partner.
Benefits of working with a SOC 2 Compliance Readiness Partner
Engaging a readiness partner before undergoing a SOC 2 audit can be highly beneficial for organizations. Here are several reasons why:

1. Expert Guidance
A readiness partner brings expertise in SOC 2 compliance and understands the intricacies of the audit process. They can provide invaluable guidance on interpreting SOC 2 Trust Service Criteria (TSC), implementing required controls, and preparing documentation to meet audit requirements.
2. Efficiency
By working with a readiness partner, organizations can streamline their SOC 2 compliance efforts. The partner helps identify gaps and weaknesses in controls early on, allowing the organization to address them proactively before the audit. This can save time and resources during the audit process.
3. Risk Mitigation
SOC 2 compliance is about ensuring the security, availability, processing integrity, confidentiality, and privacy of data. A readiness partner helps organizations identify and mitigate risks in these areas, reducing the likelihood of audit findings and non-compliance issues.
4. Tailored Approach
Every organization is unique, with different business processes, systems, and risk profiles. A readiness partner tailors their approach to the specific needs and circumstances of the organization, ensuring that compliance efforts are aligned with its objectives and operational realities.
5. Preparation for Audit Success
Engaging a readiness partner increases the likelihood of a successful SOC 2 audit outcome. By thoroughly assessing readiness, addressing deficiencies, and providing ongoing support, the partner helps the organization demonstrate its commitment to compliance and readiness to auditors.
SOC 2 compliance is increasingly becoming a prerequisite for business, especially in industries dealing with sensitive data. By achieving SOC 2 compliance with the help of a readiness partner, organizations enhance their reputation and instill confidence among customers, partners, and stakeholders.
Having a readiness partner before undergoing a SOC 2 audit can significantly improve the organization’s readiness, efficiency, and overall success in achieving compliance. By leveraging their expertise and support, organizations can navigate the complexities of SOC 2 compliance more effectively and position themselves for long-term security and regulatory compliance.
Role of a SOC 2 Compliance Readiness Partner
A SOC 2 Readiness Partner plays a crucial role in assisting organizations in preparing for a System and Organization Controls (SOC) 2 audit. SOC 2 audits are performed to assess the effectiveness of controls related to security, availability, processing integrity, confidentiality, and privacy of data within service organizations. Here are the tasks typically performed by a SOC 2 Readiness Partner:

1. Initial Consultation and Scoping
The Readiness Partner begins by understanding the organization’s business objectives, services provided, and the scope of the audit. They then work closely with the organization’s stakeholders to identify critical systems, processes, and data flows that need to be evaluated for SOC 2 compliance.
The Readiness Partner educates the client on the requirements and expectations of SOC 2 compliance and provides guidance on interpreting SOC 2 Trust Services Criteria (TSC)and standards applicable to the organization’s industry and specific circumstances.
A comprehensive gap analysis evaluates the organization’s current controls against SOC 2 requirements. The Readiness Partner identifies areas where controls are lacking, weak, or not adequately documented to meet SOC 2 standards.
4. Control Mapping
After identifying gaps, the Readiness Partner helps the organization map existing controls to SOC 2 criteria. They ensure that controls are aligned with the Trust Service Criteria (TSC) defined by the American Institute of CPAs (AICPA).
5. Documentation Review and Development
The Readiness Partner assists in creating or updating policies, procedures, and documentation to meet SOC 2 requirements. They help draft control narratives, risk assessments, and other necessary documentation to support SOC 2 compliance efforts.
6. Remediation Planning
Based on the gap analysis, the Readiness Partner develops a remediation plan outlining steps to address identified deficiencies. They prioritize remediation efforts based on risk and criticality to ensure efficient use of resources.
7. Implementation Support
A SOC 2 Compliance Readiness Partner provides ongoing support during the implementation of remediation measures. They assist in configuring systems, implementing security controls, and training staff to ensure compliance with SOC 2 requirements.
8. Internal Audit
Conducting an internal audit helps the organization simulate the actual SOC 2 audit process. The Readiness Partner assists in preparing for the SOC 2 Audit by conducting test procedures, reviewing documentation, and identifying areas for improvement.
9. Readiness Assessment Report
After completing the readiness assessment process, the Readiness Partner prepares a comprehensive report detailing findings, recommendations, and the organization’s readiness for the SOC 2 audit. This report serves as a roadmap for the organization’s SOC 2 compliance journey and helps demonstrate readiness to stakeholders and auditors.
10. Ongoing Support and Monitoring
Once the organization is prepared for the audit, the readiness partner will facilitate communication with SOC 2 audit firm, ensuring that all necessary information is provided. This includes assistance with the description criteria, furnishing evidence for controls, aiding in the collection of sample evidence, conducting walkthroughs, participating in interviews with the audit firm, and addressing any unresolved inquiries or issues raised by the audit firm.
A SOC 2 Readiness Partner plays a critical role in guiding organizations through the process of preparing for a SOC 2 audit. From initial scoping to ongoing support, they help organizations understand, implement, and maintain the necessary controls to achieve SOC 2 compliance. During your journey to SOC 2 Compliance, we recommend you consider undergoing Vulnerability Assessment and Pen Testing.Vulnerability Assessment and Pen Testing for SOC 2 Compliance
Your SOC 2 Readiness Partner may also offer vulnerability assessment and penetration testing services to help you prepare for your SOC 2 Audit and to ensure your controls are SOC 2 compliant. Here’s how vulnerability assessment and penetration testing can be integrated into the preparation for SOC 2 compliance:
1. Identify Security Weaknesses
Vulnerability assessment involves scanning systems, networks, and applications to identify security weaknesses such as misconfigurations, outdated software, and known vulnerabilities. Penetration testing takes this a step further by simulating real-world attacks to exploit identified vulnerabilities.
2. Mitigate Risks
By conducting vulnerability assessments and penetration tests, your Readiness Partner helps your organization identify and mitigate risks to data security, availability, processing integrity, confidentiality, and privacy—key areas of concern for SOC 2 compliance.
3. Align with SOC 2 Criteria
SOC 2 requires organizations to have effective controls in place to protect sensitive data and ensure the integrity and availability of systems. Vulnerability assessments and penetration tests help identify weaknesses in these controls, allowing the organization to address them before the audit.
4. Demonstrate Due Diligence
By proactively conducting vulnerability assessments and penetration tests, the organization demonstrates due diligence in safeguarding sensitive information and meeting SOC 2 requirements. This can enhance confidence among customers, partners, and auditors in the organization’s commitment to security and compliance.
5. Commit to Continuous Improvement
SOC 2 compliance is not a one-time effort but requires continuous monitoring and improvement of security controls. Vulnerability assessments and penetration tests provide valuable insights into evolving threats and vulnerabilities, enabling the organization to adapt its security measures accordingly.
While vulnerability assessment and penetration testing are not explicitly required for SOC 2 compliance, they are highly recommended practices to strengthen an organization’s security posture and readiness for the audit. By helping identify and address security vulnerabilities, these services contribute to building a robust control environment aligned with SOC 2 criteria. Therefore, a SOC 2 Readiness Partner may offer these services as part of their comprehensive approach to preparing organizations for SOC 2 compliance.
How databrackets can help you achieve SOC 2 Compliance
databrackets works in conjunction with certified CPA firms to prepare our customers to get ready for a SOC 2 Examination and obtain a SOC 2 report. Some of the services by our security experts are:
- Readiness Assessment & Recommendations
- Testing of Controls, Vulnerability Assessment and Security Risk Assessment
- Support to draft the Management Assertion for your SOC 2 Report
SOC 2 Examination by a certified CPA includes
- Determining the Trust Services Criteria
- Finalizing the SOC 2 Audit Period
- Scoping of the systems and applications
- Sampling & reviewing the evidence and policies & procedures
- Interviewing process owners
- Walkthrough of the systems/processes
- Testing the controls
- Documenting and reporting
The CPA that you chose to work with can access all your evidence in a streamlined manner on dbACE – our GRC Platform.
databrackets overview
Our team of security experts has supported organizations across a wide variety of industries to align their processes with security frameworks like HIPAA, 21 CFR Part 11, ISO 27001:2022, SOC 2, NIST SP 800-53, NIST Cybersecurity Framework, NIST SP 800-171, GDPR, CMMC etc.
We are constantly expanding our library of assessments and services to serve organizations across industries. Schedule a Consultation if you would like to Connect with an Expert to understand how we can customize our services to meet your specific requirements.
Related Links:
SOC 2 Type 2 Audit for SaaS Companies
Can you submit a SOC 2 Report instead of a Vendor Security Questionnaire?
Author: Aditi Salhotra, Digital Marketing and Business Development, databrackets.com
Aditi is a Digital Marketing and Business Development Professional at databrackets.com. She graduated with honors in Marketing from Sheridan College, Canada. In addition to her current profile, she contributes to Product Development and Content Creation. She is a strong advocate of Good Cyber Hygiene and white hat SEO techniques. She is proud of the company’s mission to safeguard organizations from cyber threats and ensure their business continuity in adverse situations.
Technical Expert: Srini Kolathur, Director, databrackets.com
The technical information presented in this blog has been carefully reviewed and verified by our Director, Srini Kolathur. Srini is results-driven security and compliance professional with over 20 years of experience supporting, leading, and managing global IT security, compliance, support, and risk assessment in fortune 100 companies. Some of his key areas of focus are SOC 2, ISO 27001, NIST 800-171, NIST 800-53, NIST Cybersecurity Framework, HIPAA, Security Risk Assessment, CMMC 2.0 among others. He is a CMMC Registered Practitioner (RP), CISSP, CISA, CISM, MBA. He is active in several community groups including Rotary International and TiE.
Is HITRUST Worth The Investment?
What is HITRUST?
HITRUST, or Health Information Trust Alliance, is a non-profit organization that uses the ‘HITRUST approach’ to help the healthcare industry control data protection standards and effectively manage data, information risk, and compliance. It’s similar to HIPAA, but instead of being written and enforced by the federal government, HITRUST is regulated by a group of healthcare professionals.
HITRUST is a way for the healthcare sector to self-regulate security practices while also fixing some of HIPAA’s shortcomings and providing a PCI (Payment Card Industry)-like enforcement system for businesses to adopt. HITRUST is a recommended framework trusted by many larger healthcare companies, health networks, and hospitals to manage risk along with other frameworks.
Why is HITRUST important?
In the United States, HITRUST is the healthcare industry’s security framework getting adopted primarily in hospitals It sets an industry-wide standard for handling Business Associate compliance. For a variety of reasons, HITRUST is slowly getting adopted in the healthcare industry along with other certifications:
HITRUST is updated daily to keep healthcare organizations up to date on new regulations and security threats. It is the most frequently updated security framework, with periodic updates and annual audit revisions. This ensures that those who follow the HITRUST CSF(Common Security Framework) work tirelessly to ensure their safety.
Some large payers need HITRUST. On February 8, 2016, five major healthcare payers assured their business associates that they would comply with the HITRUST CSF within two years. As a result, companies must consider “what HITRUST entails” and “what changes are needed to be made to achieve and maintain certification.”
HITRUST Certification has the strictest requirements with high-risk data that can demonstrate that an entity is a leader in compliance because they have the certification to back it up.
Is HITRUST worth it?
HITRUST Certification won’t be easy.
Many business associates will find it challenging to obtain HITRUST CSF certification because the vast majority may be unprepared and caught off guard. This is due to the fact that many organizations, especially smaller vendors, lack the resources to complete HITRUST CSF Certification. Organizations must not only meet the CSF criteria, but a third party must also audit them before being approved, and they must be recertified every other year.
Several businesses are taken aback by the HITRUST certification. Why?
- Firstly, the cost of assessment and assessor services are high. Budgets are often tight, and data protection may be a substantial investment as the cost might be too steep for small and medium enterprises, and HITRUST might be perceived as more expensive. For enterprises, HITRUST Certification could be seen as an investment rather than an expense
- Many customers are hesitant to invest in HITRUST because they fear failing
- A company choosing to get HITRUST certified, must first adopt the HITRUST CSF (Common Security Framework) which is updated regularly with multiple versions. You need to stay on top of the update, use the right protocol and technologies to be able to use it effectively. This may be a daunting task for many companies
- Assessment may include up to 400 control criteria and take upto 8 weeks depending on the scope and complexity of the company. This may be severely time consuming
The HITRUST Certification Fee

If you’re looking for a ballpark figure, the best guess will be $50,000 to $200,000, not including ongoing recertification costs. However, the range is so wide that it is ineffective for your business.
It depends on the assessment’s reach and the organization’s size, the state of its information system, and the steps taken to plan for a HITRUST assessment.
What exactly is included in this price?
Costs directly related to:
– The HITRUST MyCSF® gateway and services are made available
– Companies can take a readiness assessment and rating it
– Conducting a difference analysis, administering and rating a validated evaluation
Indirect costs incurred as a result of:
– Employee time spent on participation
– Security data recording and updating
– Initial setup
– Developing corrective action plans and remediation initiatives
– Assistance in locating and submitting necessary documents
Why is HITRUST Certification more expensive than other security certifications?
One must factor in the detail-oriented approach, thoroughness, and dependability.
A thorough examination
Depending on the company’s risk profile, a single HITRUST assessment may include up to 400 control criteria. This is in addition to the three forms of protection required by HIPAA regulations, the 12 PCI DSS compliance standards, COBIT’s five domains, 37 processes, and the 80-100 controls included in a SOC 2 audit.
The HITRUST CSF blends these and other regulatory standards into a single, overarching risk management and enforcement program, which is one of the most tangible benefits of the framework. It combines information management, financial services, technology, and healthcare standards. As a result, businesses will streamline their enforcement processes, resolve security concerns in all sectors, and reduce the time and expense associated with maintaining compliance with multiple standards.
Detail-oriented approach
Each control in your organization’s assessment must be reported, assessed, checked, and verified by an accredited external assessor before being evaluated by HITRUST. In addition, each control must be assessed using the HITRUST Maturity Model, which has five levels.
The HITRUST CSF certification process covers much more ground than any other security evaluation. In most cases, 2,000-2,500 separate data points are examined. Throughout this phase, an average of 1.5 hours per control is spent, with the number of controls assessed varying depending on the organization’s size, risk profile, and scope.
Dependability
The HITRUST CSF system was created to give enforcement programs more structure and continuity. Recent enhancements have also increased scoring accuracy over time and between internal and external assessors.
HITRUST has strict standards for the assessor firms and experts involved in its commitment to solid assurance. Firms must apply for and receive approval from HITRUST to conduct assessments and services related to the CSF Assurance Program and work hard to retain that status.
Certified CSF Practitioners (CCSFP) are HITRUST Approved External Assessors responsible for assessing and validating security controls. They must complete a training course, pass an exam, and retain certification through regular refresher courses. HITRUST helps organizations ensure the evaluation and certification process is accurate through service.
Can you have a data breach after a HITRUST Certification?
While HITRUST released a statement in its defense that “the healthcare payer did not have a breach in any system or area of the organization that was within the scope of its HITRUST CSF Certification,” some security experts did question the significance “what did it mean to be HITRUST certified?” given the scale and sheer magnitude in the numbers.
HITRUST Alternatives
The HITRUST CSF is a certifiable and widely accepted security framework with a list of prescriptive controls to demonstrate HIPAA compliance. However, as alternatives to HITRUST, several SMEs comply with other security governance frameworks like the National Institute of Standards and Technology [NIST], HIPAA, SOC Reports – SOC 1, 2, and 3 Form 1 and 2 and ISO 27001 Certification.
NIST is a set of voluntary guidelines, and processes that companies use to reduce the risk of a cybersecurity threat. It aims to improve security and resiliency by implementing 108 security controls to achieve NIST compliance.
Many HIPAA requirements may not be understood in accordance with their intended objectives. HITRUST aims to provide an integrated and holistic approach to demonstrate compliance with HIPAA security requirements.
HIPAA is a federal law with national standards to protect sensitive patient health information from being disclosed without the patient’s consent or knowledge.
Based on the certification goals and requirements of our clients, we offer alternative frameworks NIST, ISO 27001 or SOC 2 certifications. Different certifications involve different costs and levels of efforts, so it is imperative to consider your size, requirement and budget before you seek certification. IF you company falls under a broad range of industries or comes under a regulated industry, SOC 2 may be the best option. If your company processes electronic health information, HITRUST may be the better option.
Talk to us to understand your certification category and know more information
About databrackets
databrackets certified privacy and security professionals could help your organization comply with a range of Certifications and Compliances that include HIPAA/HITECH, PCI Data Security, CCPA, OSHA, GDPR, Penetration Testing, FDA CFR Part 11, ISO 27000, Cloud Security Management, NIST Framework, Cybersecurity Framework, SOC Certification, Third-party Assessment, NYDPS Cybersecurity Series, ISO 17020, and ISO 27001.
databrackets assists organizations in developing and implementing practices to secure sensitive data and comply with regulatory requirements. By leveraging databracket’s SaaS assessment platform, awareness training, policies, and procedures, and consulting expertise, you can meet the growing demand for data security and evolving compliance requirements more efficiently.
American Association for Laboratory Accreditation (A2LA) has accredited databrackets for technical competence in and compliance with the Inspection Body Accreditation Program.
databrackets has been accredited by the American Association for Laboratory Accreditation (A2LA) as a Cybersecurity Inspection Body for ISO/IEC 17020:2012 vide its Certificate Number: 5998.01.
The Cybersecurity Inspection Body Program accreditation provides added trust and assurance in the quality of assessments performed by databrackets. A2LA’s third-party accreditation offers an independent review of databrackets’ compliance to both ISO/IEC 17020 (Requirements for the operation of various types of bodies performing inspections) as well as competence in technical program requirements for the desired scope of accreditation (I.e. SOC II, HIPAA/HITECH, PCI, etc.).
databrackets received accreditation by the International Accreditation Service (IAS] to provide ISO/IEC 27001 Certification for Information Security Management Systems (ISMS) and joins an exclusive group of certification bodies.
To learn more about the services, read here.
Comparing NIST, ISO 27001, SOC 2, and Other Security Standards and Frameworks
We, at databrackets, with the help of our partners and consultants, have compared popular security standards and frameworks (mandatory and voluntary). Our analysis focuses on practical aspects you need to consider before implementing the controls under each framework.
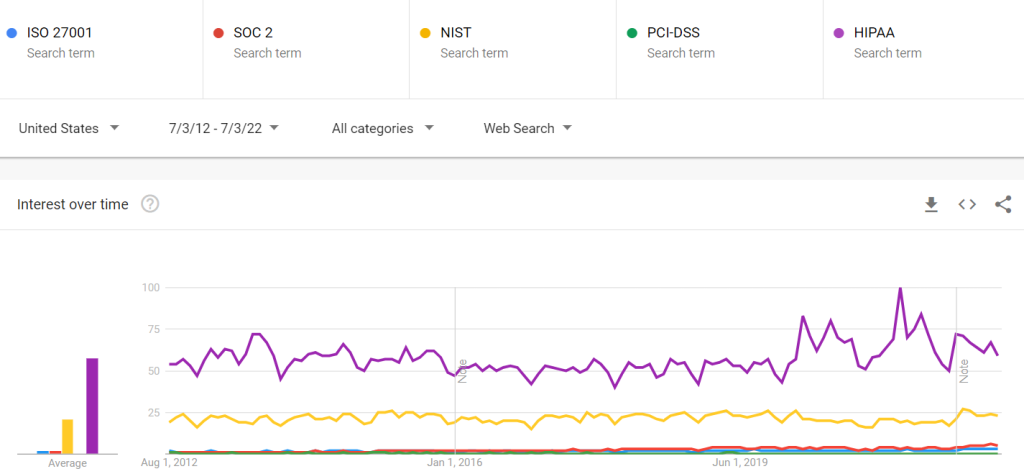
To begin our comparison, we looked at Google Trends for the interest in these security frameworks over the last decade.
Comparing Security Frameworks
The comparison parameters in the charts below focus on the information you need to get an overview of the security standards and their relevance to your organization.Key Features | ISO 27001 | SOC 2 | NIST Standards | PCI-DSS | HIPAA / HITECH | Other Standards/ Frameworks (including FedRamp, CSA, HITRUST, Shared Assessments, etc.) | Notes |
|---|---|---|---|---|---|---|---|
Certification | Yes | Yes | Not Applicable. You can get attested for compliance by a third-party. | Yes | There is no agency authorized to certify HIPAA compliance. | Yes | You need to engage the certifying bodies/ approved vendors. |
Approach | Risk-based | Controls-based | Controls-based | Controls-based | Controls-based | Maps to individual frameworks of each standard body | |
Principle | Information Security Management Systems | Trust Services Criteria & Ethics | Control Families | PCIDSS standard | HIPAA rules including Technical, Administrative and Physical Safeguards | Depends on the individual frameworks of each standard | Technology platform specific controls are not covered by the standards /certification bodies |
Certification Method | Authorized Certification Bodies | Authorized CPA Firm (Readiness Assessment can be done by a vendor) | Self (Audit and Attestation can be done by a third-party) | Authorized firm who have PCI-QSA Certified | Self (Audit and Attestation can be done by a third-party) | Third-party vendors | Third-parties require accreditation to issue certification |
Best Suited For | Service Organization | Service/Product Organization | Different industries require different levels/standards of compliance | Service Organization | Healthcare, SaaS, and any organization handling Protected Health Information of US Citizens inclduing vendors handling PHI | Service/Product Organization | Some sort of security and data privacy certification is becoming a part of most industries |
Popular in … | International | Companies operating in North America | US Federal/ Commercial / Manufacturing | International | USA | Companies operating in North America | |
Customer Acceptance (Customer Requirements) | Preferred (Mandatory in some cases) | Preferred (Mandatory in some cases) | Not Mandated | Preferred (Mandatory in some cases) | Mandatory | Depends on the Industry and marketplace where business is conducted | |
Duration | Point-in-time | 6-month period(Type 2) | Point-in-time | 3-6 Months | Point-in-time | Point-in-time | Surveillance audit is in place for most of the certifications |
Certification Frequency | Every 3 years with annual surveillance audits | Annual | Not Applicable | Annual | Annual | Mostly Annual | |
Cost | $$ | $$$ | $$ | $$$ | $$ | $$$ (HITRUST certifications cost 50k -200k) | Engaging an experienced vendor helps to ensure documentation and audit support. This saves cost in the long run. |
Below is a quick summary of each security standard and framework:
NIST Security Standards are based on best practices from several security resources, organizations, and publications. They were designed as a framework for federal agencies and programs requiring security measures. Several non-federal agencies have also implemented these guidelines to showcase that they comply with authoritative security best practices.
NIST Special Publication 800–53 is the most popular among the NIST security series. It provides the steps in the Risk Management Framework for security control selection for federal information systems. This is in accordance with the security requirements in Federal Information Processing Standard (FIPS) 200. The NIST Cybersecurity Framework (NIST CSF) has also attracted a lot of interest and attention from a variety of industries.
NIST has released the final version of Special Publication (SP) 800–219, Automated Secure Configuration Guidance from the macOS Security Compliance Project (mSCP). Security Professionals can leverage the macOS Security Compliance Project (mSCP) to secure and assess macOS desktop and laptop system security in an automated manner.
ISO 27001, is a more risk-based standard for organizations of all shapes and sizes. Although there are more than a dozen standards in the ISO/IEC 27000 family, ISO/IEC 27001 is well known for defining the requirements for an information security management system (ISMS). ISO 27001 enables and empowers organizations of any kind to manage the security of assets such as financial information, intellectual property, employee details, or information entrusted to third parties. The latest update to ISO 27001 is scheduled to be released in late 2022.
reports assess the security controls of a Service Organization in accordance with AICPA’s Trust Services Principles: Security, Availability, Processing Integrity, Confidentiality and Privacy.
SOC 2 compliance is often included as the eligibility criteria for SaaS and other service providers as they bid for B2B contracts. Type 1 and Type 2 reports meet the needs of a broad range of B2B customers who want assurance about the security of their customer data.
HITRUST stands for the Health Information Trust Alliance. A HITRUST certification by the HITRUST Alliance enables vendors and covered entities to demonstrate compliance with HIPAA requirements based on a standardized framework.
The Health Insurance Portability and Accountability Act of 1996 (HIPAA) is a federal law that requires the creation of national standards to protect sensitive patient health information from being disclosed without the patient’s consent or knowledge.
The Department of Health and Human Services (HHS) Office of Civil Rights (OCR) allocated a proposed rule for changes to the act in December of 2020 and a Final Rule is expected in 2022 with the following changes:
Increased Patient Access — the HIPAA Right of Access into the HIPAA Privacy Rule allows individuals to be more in control of their health and well-being decisions, which includes but not limited to:.
- Allow patients to inspect the medical record PHI in person and/or take notes or photos
- Reduce the time needed to provide access to PHI from 30 to 15 days
- Allow patients to request a transfer of their PHI to personal health applications.
- To post estimated fee schedules for PHI access and disclosures
The Payment Card Industry Data Security Standard (PCI DSS) is a set of security standards governed by the Payment Card Industry Security Standards Council (PCI SSC). This framework has been designed to secure credit and debit card transactions against data theft. PCI-DSS is a requirement for any organization that processes credit or debit card transactions. PCI certification is also considered the best way to safeguard sensitive data and information.
The Consensus Assessments Initiative Questionnaire (CAIQ) v3.1. offers an industry-accepted way to document what security controls exist in IaaS, PaaS, and SaaS services, providing security control transparency. It provides a set of objective questions to a cloud provider to ascertain their compliance with the Cloud Controls Matrix (CCM).
The Federal Risk and Authorization Management Program (FedRAMP) is a government-wide program in the US that provides a standardized approach to security assessment, authorization, and continuous monitoring for cloud products and services. FedRAMP enables agencies to rapidly adapt old, insecure legacy IT to mission-enabling, secure, and cost-effective cloud-based IT.
Shared Assessments provide the best practices, solutions, and tools for third-party risk management to create an environment of assurance for outsourcers and their vendors.
How databrackets can help you comply with security regulations
databrackets specializes in assisting organizations to secure sensitive data and comply with regulatory requirements. By leveraging databrackets’ SaaS assessment platform, awareness training, policies, procedures, and consulting expertise, our customers and partners are meeting the growing demands for data security and evolving compliance requirements more efficiently. Contact us here to learn more.


